Applications that you download and install from Play Store or from the web are displayed on the Apps screen. From the Home screen, ta p Apps. From the Apps screen, you can:. Move between screens: Just slide your finger left or right until the next screen appears so you can browse all apps on your tablet. Dialogic Service Center provides access to service and support contracts, support contact information and technical help information. SS7 is not a software, it's a protocol that connects Telecom Companies together. You can gain access to SS7 by buying Tactical Surveillance Software Online. But it's not cheap, 3 Months of access will cost you 39.000$. With this access you can int. A complete, practical guide to the world's most popular signaling system, including SIGTRAN, GSM-MAP, and Intelligent Networks. Provides in-depth coverage of the SS7 protocols, including implementation details Covers SS7 over IP (SIGTRAN) using real-world examples Covers SS7/C7 from both a North American and European perspective, providing a broad international understanding of the technology.

SS7 hack explained
Technology is, in its nature, developing based on current progress. Sometimes it is worth going back to the blue box era to discover something in today's world. More or less recent scandals involving NSA's practice to track, listen, and intercept communication without authorisation made a splash, but not many took the time and effort to understand the magic behind. Kudos for Washington Post: they went looking into this.
After little research taking me 50 years back in time, I will explain the technology behind and demonstrate that one does not need NSA resources or an army of hackers to repeat the trick on you.
The calling protocol that is used for one network to 'talk' to another was developed in 1970's and is called SS7. The protocol was somewhat refined around 2000 with a SIGTRAN specification, which made it IP network environment friendly. This, however, meant that all the weak links on the upper level of SS7 infrastructure were carried over.
Picture that the communication is made possible not by one, but in fact several hundreds of links, which result a chain that triggers phone on the other end of your call ringing. Referencing back to my earlier post on 'Evolution of Authentication', I would like to demonstrate that the same principle of security level assessment applies here: the chain is as safe as it's weakest link. Consider WhatsApp hacking methods, message virus trends, phone number exploits, Skype lock services.
During my time in Deutsche Telekom Consulting, I was involved in review of a number of networks (fun times included climbing down sewers following copper lines laid there in 50s-60s-70-s, which were used by corporations and governments in 2003-2004 and likely still to be in place). The hardware and software providers vary from network to network and are extremely segmented, which leads to a simple result: they have to keep their chains wide open to make sure that the next chain link can integrate.
So did anyone know about these vulnerabilities until 2013? In short: of cause. First reference I have discovered dates back to a report published in 2001, which I (admittedly) could not read to full extent due to my neglected Swedish. Google Translate may help you.
SS7 hack explained
Technology is, in its nature, developing based on current progress. Sometimes it is worth going back to the blue box era to discover something in today's world. More or less recent scandals involving NSA's practice to track, listen, and intercept communication without authorisation made a splash, but not many took the time and effort to understand the magic behind. Kudos for Washington Post: they went looking into this.
After little research taking me 50 years back in time, I will explain the technology behind and demonstrate that one does not need NSA resources or an army of hackers to repeat the trick on you.
The calling protocol that is used for one network to 'talk' to another was developed in 1970's and is called SS7. The protocol was somewhat refined around 2000 with a SIGTRAN specification, which made it IP network environment friendly. This, however, meant that all the weak links on the upper level of SS7 infrastructure were carried over.
Picture that the communication is made possible not by one, but in fact several hundreds of links, which result a chain that triggers phone on the other end of your call ringing. Referencing back to my earlier post on 'Evolution of Authentication', I would like to demonstrate that the same principle of security level assessment applies here: the chain is as safe as it's weakest link. Consider WhatsApp hacking methods, message virus trends, phone number exploits, Skype lock services.
During my time in Deutsche Telekom Consulting, I was involved in review of a number of networks (fun times included climbing down sewers following copper lines laid there in 50s-60s-70-s, which were used by corporations and governments in 2003-2004 and likely still to be in place). The hardware and software providers vary from network to network and are extremely segmented, which leads to a simple result: they have to keep their chains wide open to make sure that the next chain link can integrate.
So did anyone know about these vulnerabilities until 2013? In short: of cause. First reference I have discovered dates back to a report published in 2001, which I (admittedly) could not read to full extent due to my neglected Swedish. Google Translate may help you.
It was also made public by Tobias Engel during a Chaos Computer Club Congress held in 2008, when Tobias made a live demo of tracking abilities:
A white paper on SS7 hack SS7: locate track manipulate (pdf file; original here)
And, of cause, it was most widely reported during NSA scandal involving Edward Snowden, that revealed how NSA was exploiting the weaknesses of SS7 to create a very intelligent and complex series of solutions enabling them to simultaneously track and analyse millions of citizens without their nor carrier's knowledge or approval.
SS7 hack software
So what does one require to make this work? The list is quite short:
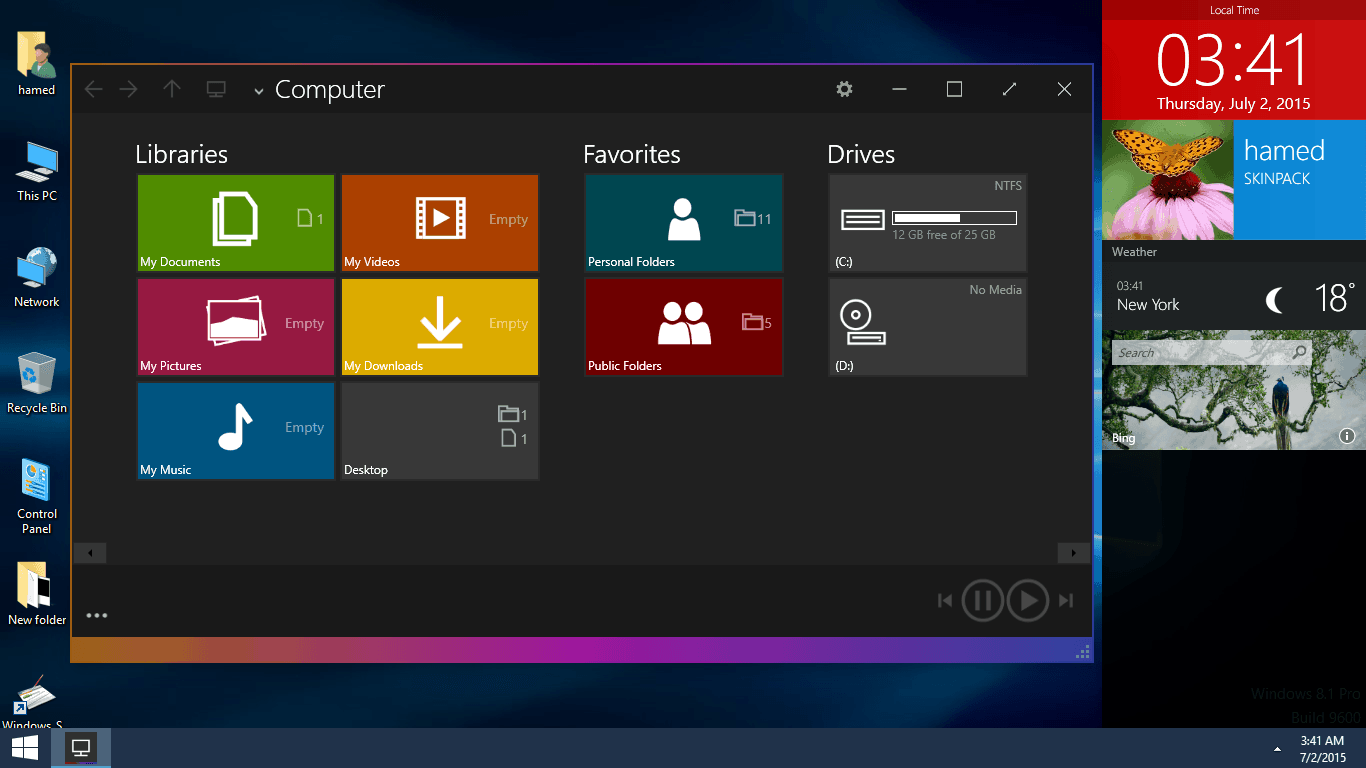
- Computer
- Linux OS
- SDK for SS7
Ss7 Download For Windows 10 Xp
Apart from the computer itself, remaining ingredients are free and publicly available on the Internet.
It may have slipped under your radar, but apparently now there is a legal way to use this technology to track anyone worldwide, and NSA is not involved at all: the service offering is open to public and provided by a NASDAQ listed Verint Systems Inc. (NASDAQ: VRNT). In their product description, which was made public, they refer to the system as 'Skylock'. During search I even stumbled upon a certification of encryption capabilities of this product by NIST (certificate scan).
Ss7 Attack software, free download
Verdict? Abandon illusions of privacy if you still had them.
Sources:
- A study of Location-Based Services including design and implementation of an enhanced Friend Finder Client with mapping capabilities (Aug. 2001)
- Uncut video of Tobias Engel's speech 'Locating mobile phones using signalling system #7' at 25th Chaos Computer Club Congress (12/27/2008 21:45:00)
- Skylock product description (2013)
Disclaimer: this article is a warning to regular citizens about low technological barrier protecting their privacy specifically in relation to mobile phone hacking using ss7 protocol. It is not a guide to hack-a-phone. I will intentionally leave a few aspects uncovered. I urge all readers NOT to use this technology and hope that the solution to restrict this ability to track phones will be implemented soon.
